**“Preventive measures for failures I haven’t actually experienced” also count as ideas, so I’m including them here.
I’ve only written about forty so far, but I’ve decided to publish them anyway.」
—–
050.How to open a file in Command Prompt when the entered string matches part of the file name
for %f in (test) do start “” “%f”
049.A command that launches WinMerge from the command line and visualizes the differences across a large number of files all at once
WinMergeU.exe Filename01.txt Filename02.txt /ub /or HTML_Filename01.html
048.VBA: Generate Excel Sheets from Common Filename Substrings
047.Clear the contents of all sheets in a multi-sheet Excel workbook, including formatting
046.Generate a VBA script in Excel that lists all sheet names
045.Use a Large File Download from a Web Server for Network Failure Testing!
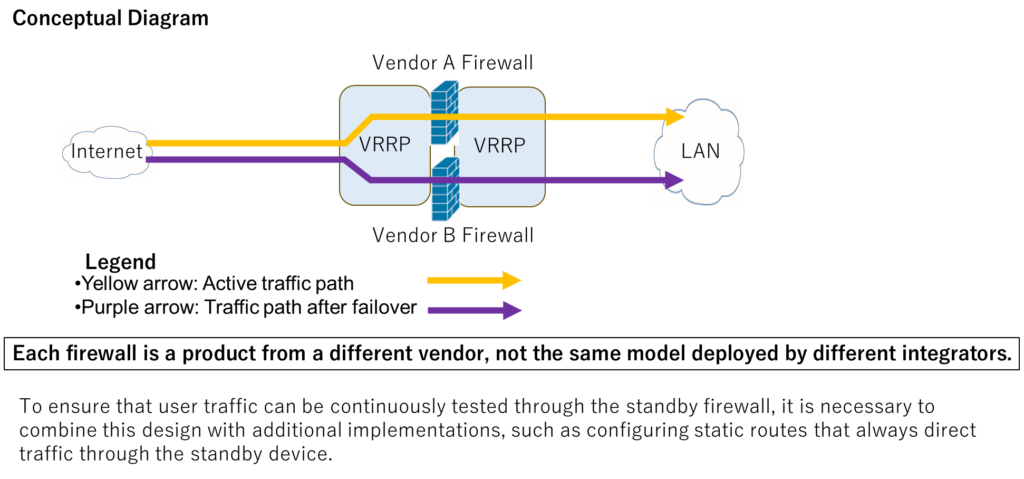
After running failure tests on firewalls and load balancers,
it sometimes turns out after the fact that TCP sessions were not actually being handed over correctly.
This seems to be an issue limited to certain less popular models, such as “xx” and “yy.”
Here’s the countermeasure.
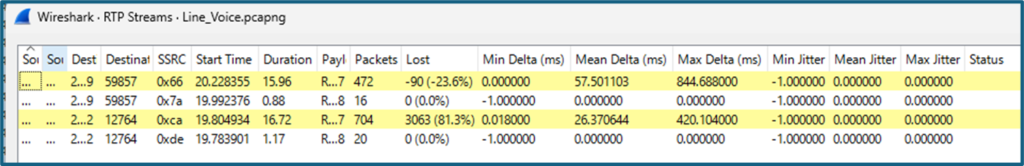
If, during failure testing, you use file downloads from a Web server instead of (Ex-)Ping,
you can detect issues before handing the system over to the server/application team.
* If you set the top page of the test Web server to a large file (which you can generate instantly from the command prompt),
accessing it will automatically start the download.
* Record the recovery-time evidence with Wireshark.
* You can do the same thing with httping, but since the SYN is sent only on the first request (meaning it’s treated as the same session), and the send interval cannot be set below 1000 ms, it may not be suitable for tight-interval testing.
044.During failures, the fastest to recover is a static route (because you only need to care about the HSRP timers).
However, after the system goes into operation, it requires someone who has all the IP addresses memorized—including their history and context.
This increases operational dependency on specific individuals and raises the risk of personnel bottlenecks.
Here’s the countermeasure.
If you delegate IP address management to a local generative AI system that sends no data externally, the disadvantages can be greatly mitigated.
To put it bluntly, the greatest benefit is that all information is presented in clear, readable natural language.
* When documenting recovery behavior, the Layer-1 keepalive should also be included among the timing parameters in the design documents.
043.Is that power cable on the A feed or the B feed?
All you need to do is connect the PLC to the A feed only and run a Ping.
If you attach a DHCP server, you can simply check whether the client receives an IP address or not to determine the result.
042.When checking for defective physical ports on a newly purchased switching hub,
are you testing by plugging and unplugging a single LAN cable?
There is a faster and far more accurate method.
The answer is: write the code in TeraMacro.
041.Do you really need those expensive Wi-Fi quality tests performed by external vendors?
If all you need to confirm is the network-side quality, then verifying that the TCP/IP layer is performing adequately should be enough.
In most cases, you can simply run a Ping test.
* That said, our company does own several spectrum analyzers, so we can bring them on-site if needed.
040.Automating network vulnerability testing—using an official .org tool (not some suspicious freeware)—
wouldn’t it be great if all the data collection were finished overnight while you sleep?
* It also reduces labor costs.
(Although the analysis itself won’t be done overnight, the report can be generated automatically.)
039.Wouldn’t it be convenient if you could bulk-replace contents in Excel
(with up to 500 different patterns in a single run)?
It’s possible with VBA—just one line of code per word.
038.Wouldn’t it be convenient if you could extract only what you need from a large number of configuration files,and then open the file containing that string just by double-clicking?
* This is done using the Japanese freeware “Sakura Editor.”
037.Let’s reduce overtime and enrich your personal life through keyboard shortcuts.
If you’ve prepared the VBA code in advance,
then all you need is: Alt+F11, F7, Ctrl+V, F5—
and if the code operates on all sheets, it’s even faster.
It’s a shame there isn’t enough space here to explain it in detail.
For everyday use, you can rely on things like:
Ctrl+Page Up / Ctrl+Page Down,
Ctrl+Arrow keys,
Ctrl+Shift+Arrow keys,
or Shift+Arrow keys ⇒ F2 ⇒ Ctrl+Enter—
the point is simply to reduce how often you touch the mouse.
If you can shave just 1 second per task, then after 1,000 repetitions that’s 1,000 seconds saved.
If you have 1,000 employees, that’s 1,000,000 seconds in labor costs reduced.
And that’s before you even factor in the overtime pay premium.
036.What exactly is “efficiency”?
I personally call it “acceleration.”
You can only estimate it in advance by intuition or experience,
but I make a point of expressing and proposing it using concrete numerical gains—
such as “We can accelerate this by 100× to 1,000×”
or “A 2–3× speed-up is achievable.”
035.Since we all know it’s going to fail anyway—
because obviously we’re about to fall straight into a trap—
I sometimes say, “Why don’t we just have lunch first?”
And of course, the one time that suggestion gets rejected is exactly when my bad feeling turns out to be 100% correct.
It’s like the universe saying, “I tried to warn you, buddy.”
034.Since it’s obviously going to fail—
because we know we’re about to get stuck—
let’s avoid any “one-shot, no-retry” attempts.
You have to at least try everything you reasonably can and still fail;
otherwise, people won’t feel any sincerity when you apologize.
No “tragic backstory,” no credibility.
033.Let’s prepare a standard template for failure-point diagrams ahead of time.
Create a set of icons with numbered failure points,
making sure there are no missing or duplicate numbers.
Once that’s ready, you can simply cut & paste, and numbering mistakes won’t happen anymore.
* And… if this very thread ends up having missing or duplicate numbers, my apologies in advance.
032.The wages for the customer-facing team
are probably higher than those of the technical team.
Just one mistake on-site can cost an enormous amount of time and money.
(And the people who end up apologizing are always the upper tier.)
Have you ever calculated the impact of mistakes
beyond your own team’s boundaries?
031.Even a small team needs a profit plan.
The profit plan you create right now is what will elevate your position in the future.
Because building a profit plan for your current project
is essentially the same as building a profit plan for your life.
030.When your schedule slips,
are you also calculating the labor costs of the teams behind you?
Even if they’re just waiting around,
their wages are still being paid.
029.If possible, I’d rather avoid “instant kills” using knowledge and experience.
When we don’t even know whether something is possible—
when we’re on the edge and the client is on the edge—
isn’t that what real collaboration with a customer looks like?
028.Saying “Let’s start with what we can do” is a mistake.
There are plenty of things that we can do but are meaningless.
Instead, look for actions that actually matter—
and when you can’t do them, start thinking about how to make them possible.
I believe that this kind of repeated effort is what creates overwhelming value.
027.How do you make something possible?
The first step is simply to decide that you’re going to do it.
026.When you’re worrying that you “might not be able to do it,”
just decide that you’ll pull it off anyway.
025.Parameter sheets tend to get scattered across multiple Excel sheets.
Why not generate them with VBA instead?
The biggest advantage is that every parameter ends up aligned in a single column on a single sheet.
024.When traveling for on-site work as an infrastructure engineer,
book a hotel the night before—preferably near an electronics store.
Most of them will at least carry USB–serial converters.
They probably won’t have rollover cables, but you can usually find JJ adapters.
They also tend to stock generic power adapters.
023.When traveling for work, avoid taking flights late in the day.
There was actually a case where a fire broke out near the airport,
and the delay caused the flight to miss the destination airport’s operating hours,
forcing the plane to turn back halfway.
022.Why not at least submit the access request one extra day in advance?
When your work runs late, when exactly will you file the access request for the next day?
And even if you submit it first thing in the morning, what time will you actually be allowed in?
Are you really going to wake up your manager or the prime contractor to rush the approval?
Finishing ahead of schedule will always earn you a higher evaluation.
021.Rather than clinging to field work, aim for a promotion sooner.
In meetings, you can see and hear all kinds of incidents from the field—
because trouble, of course, always happens out there.
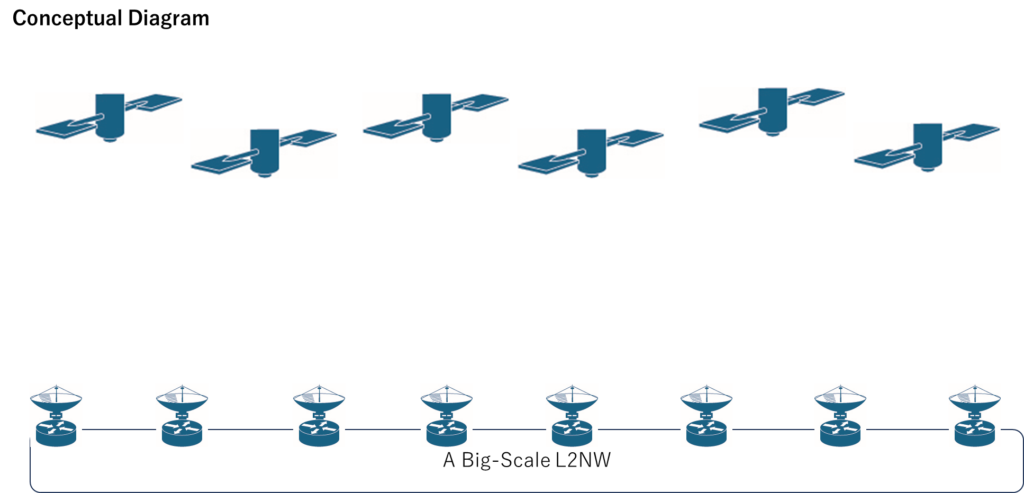
020.For active–active circuit redundancy,
if your existing routers are Cisco,
wouldn’t implementing GLBP basically solve the problem?
019.Before saying “the circuit is slow,”
there are a few things you should check.
- Are you accidentally double-encrypting the traffic?
- When you switched to a longer encryption key, do you know how much the MTU increased?
- And are you thinking, “Well, the encryption got stronger, so of course the communication got slower”?
—Are you sure that’s the right assumption?
018.Besides bandwidth guarantees,
do you know of any circuits that also provide an RTT guarantee?
For remote-work environments, capacity alone isn’t enough.
And to go a step further, OCSP is going to become increasingly important in the coming years.
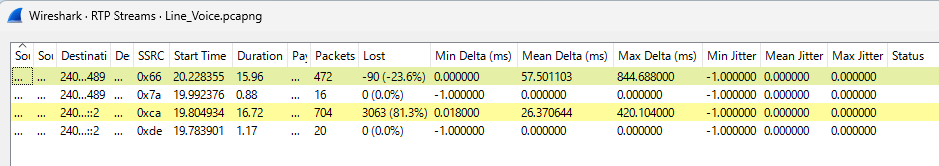
017.You—start using Wireshark.
…Just saying it in my best Mas Oyama voice.(NOBUTATU-OHYAMA)
A joke that works only in Japan.
016.You—go back to your childhood and start playing walkie-talkie.
(Not the metal-to-fiber media converters.)
Here’s why:
015.Getting used to one-way communication will improve your listening skills.
014.During failure testing, I said “I’m not angry!” in the old KORIKI comedy style—
and that’s when I felt a huge generation gap.
It turns out younger engineers don’t know him at all.
(A joke that works only in Japan.)
013.I referenced the old “KIRETENĀI” razor commercial,
and it completely fell flat in a field full of younger engineers.
(It’s a joke that doesn’t land even with young people in Japan.)
012.Sliding windows—and various keepalive-related source flows—often fall into the gap between the server team and the network team.
Why don’t we, on the network side, just take ownership of them?
Things will get resolved much faster that way.
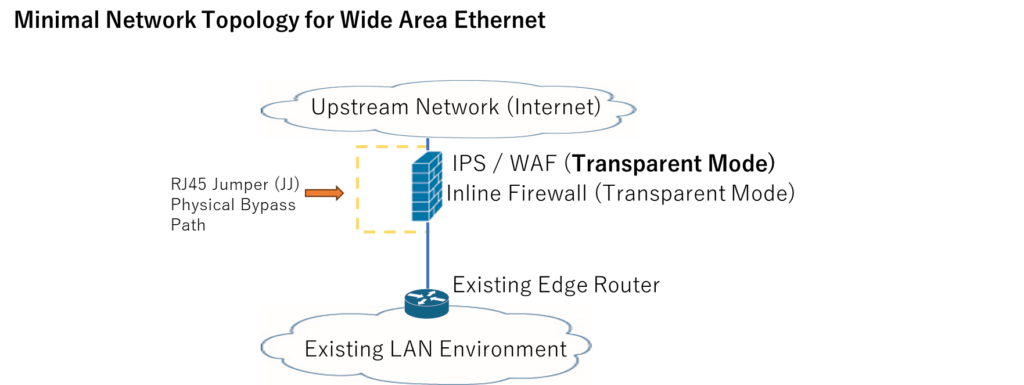
011.For your IPS or WAF,
what destination are you allowing for signature-update DNS queries?
If you’re permitting them using fixed destination IP addresses,
you’re at risk of being left behind by the times.
010.Whitelist-based web filtering can sometimes be a poor match for cloud services.
As for the reasons and the solutions—
I’m not going to write those here for free.
(And yes, the Japanese phrasing forms a 5-7-5 haiku.)
009.About the part where I said I wouldn’t write it for free—
I felt a bit guilty, so I tried generating a “shōbai da mono” line using a Mitsuo-style generator.
But I ended up losing the image.
Do you know AIDA MITSUO? AIDA is not “Ada,” you know.
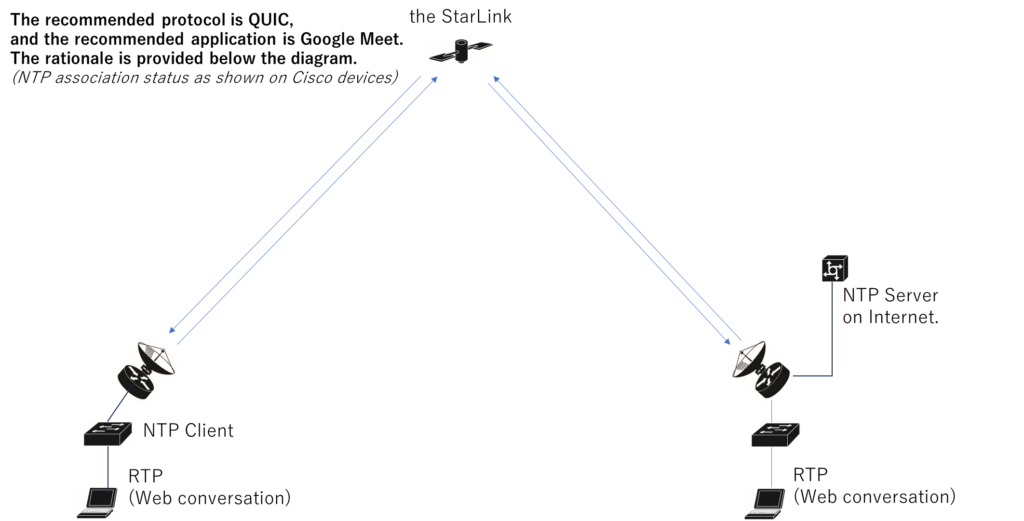
008.With the growing adoption of HTTP/3 and QUIC,
web filtering may eventually lose much of its effectiveness.
When that happens, C&C (command-and-control) control will likely become the mainstream approach.
Although, attacks that route through intermediate stepping stones will still be difficult to prevent.
007.And that would mean routing methods that rely on DNS would also end up being restricted.
As a result, we may start seeing more cases where
Windows Update simply stops working—
all because the necessary traffic can’t get through.
006.Translation in progress… Coming soon.
005.Block attachments in Outlook that are not on an approved whitelist.
The linked page is in Japanese.
You should be able to read it by using your browser’s translation feature.
004.Use show proc cpu and apply a binary-search approach to determine which process is consuming CPU.
You simply change the ACL used for L3 processing:
first set the first half of the ACL entries to deny and see if anything changes.
If nothing changes, switch to denying only the second half,
and repeat the process.
003.Using Analog Noise Cancellers in Call Centers
AI-based noise cancellation sometimes fails to remove the voices of people standing behind the operator.
In such cases, an analog noise canceller that inverts the phase of the unwanted sound can be effective.
002.Wi-Fi Troubleshooting
I’ll include some notes about the time I measured weather-satellite signals.
Yes, yes… that’ll be posted later, of course.
001.Reflection:
I used to think Ethernet signals were square waves.
The reason for the misunderstanding?
Because I actually tested it with my own hands.
“`html
Technical Inquiry
If this article relates to your network architecture, security design,
or infrastructure modernization, feel free to contact us.
Email:
contact@g-i-t.jp
Related Architecture Solutions
Typical network architecture solutions designed and implemented by GIT.
These patterns are derived from real enterprise environments and long-term operational experience.
View Network Architecture Solutions
Back to Home
“`