FortiGate IPS Intrusion Prevention Audit Results
The system architecture is as follows.
We use Nmap, a globally standard penetration testing tool, to perform penetration testing of the web server.

Results of inspection without IPS (measured with Wireshark)
Server-side Wireshark display: showing only HTTP traffic with filter
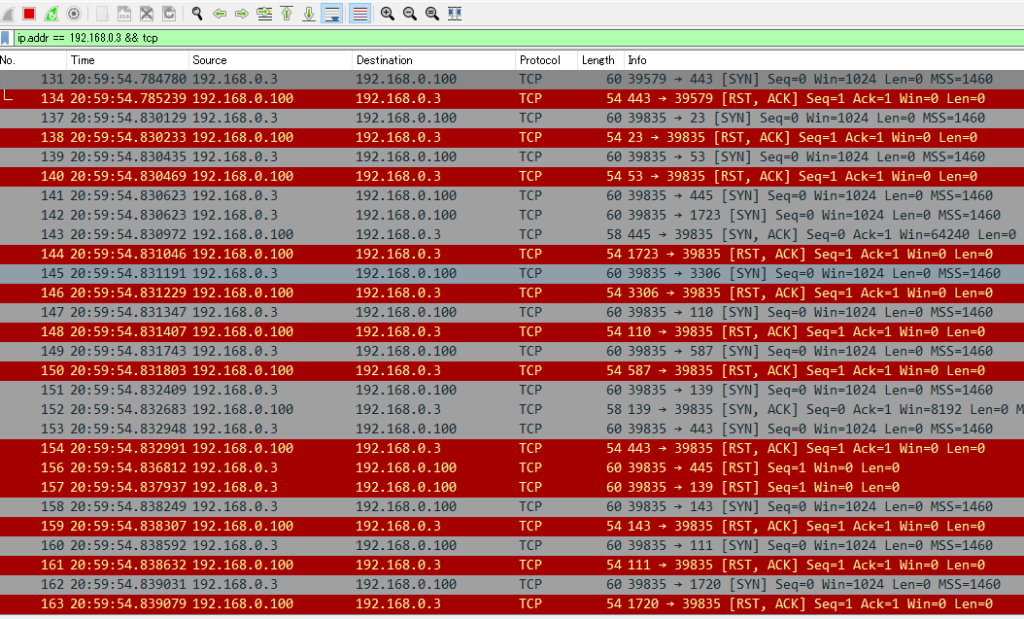
Results of inspection with IPS (measured with Wireshark)
Server-side Wireshark display: only HTTP traffic is shown using the filter (no packets are shown)
This means that the FortiGate IPS detected and blocked the HTTP-based attack traffic before it reached the web server.

*This document is intended for external explanation purposes, therefore, Wireshark uses a display filter limited to the HTTP protocol.
Detailed verification results, including lower layers (TCP/TLS, etc.), can be explained individually.
Contact information:
If you would like to know how to configure the system, please contact us at the address below.
Contact for Deployment Validation
I can communicate verbally in English using an automatic speech recognition translation tool.
The UTM appliance can be purchased from Amazon.
I only offer remote configuration and design.
My recommended design principles are as follows:
Transparent Mode
Advantages:
There is no need to publish the global IP address on the internet.
This way, the FortiGate appliance is not exposed to attacks from the internet.
The appliance is simply placed between the internet port of an existing router and the line termination device.
The recommended physical connection is as follows:
The “accessory” acts as an L2 switch and a next-generation firewall (NGFW).
