A Network That Keeps Operating Even Under Wartime Conditions
Concept: Security Events Directly Trigger Network Path Control
In environments where service continuity is critical, the network must be able to continue operating even when key infrastructure components become compromised, overloaded, or untrusted.
This design proposes a mechanism in which security-relevant syslog events act as triggers for immediate and deterministic network path changes.
When predefined security conditions are met, an automated control sequence modifies VRRP priority values to shift the active gateway role to an alternate firewall or IPS device from a different vendor.
This allows the network to continue operating while isolating or bypassing potentially compromised equipment.
The intent is not only failover for availability, but failover for trust preservation.
Architecture Overview
The system consists of four logical layers:
- Event Detection Layer
Security-related syslog messages are received from firewalls, IPS devices, and core infrastructure.
Only specific, pre-correlated events are treated as actionable triggers. - Decision Layer
A control host—preconfigured and isolated—evaluates whether the received events meet the threshold for failover.
Conditions may include:- Severity level
- Repetition count
- Source correlation
- Time window thresholds
- Control Execution Layer
Once validated, an automated macro or scripted control process connects to network devices and modifies VRRP priority values.
This forces the gateway role to migrate from the primary security appliance to an alternate vendor’s firewall or IPS path. - Stability and Recovery Layer
To prevent oscillation or repeated failover:- Cooldown timers are applied
- Manual confirmation may be required for restoration
- Health checks confirm stability before reverting
Why VRRP Priority Manipulation
VRRP provides a deterministic and vendor-neutral mechanism for gateway role selection.
By adjusting priority values instead of shutting down interfaces, the system can:
- Preserve routing consistency
- Maintain predictable failover timing
- Avoid full routing reconvergence
- Keep recovery reversible
This approach allows failover logic to be externally controlled while still relying on standard L3 redundancy protocols.
Cross-Vendor Failover as a Security Strategy
Traditional high-availability designs assume identical hardware pairs.
However, in adversarial conditions, homogeneous redundancy can become a liability.
A heterogeneous security path offers:
- Reduced single-vendor attack surface
- Independent firmware and control planes
- Divergent vulnerability profiles
- Operational resilience against targeted exploits
Failing over from one vendor’s device to another is not only redundancy—it is defense diversity.
Control Point Design Considerations
The control host that initiates VRRP changes must be:
- Isolated from general user networks
- Hardened and access-restricted
- Able to operate even during partial infrastructure failure
- Capable of manual override
Automation should assist the operator, not replace situational awareness.
The system is designed so that human authority remains intact even during automated transitions.
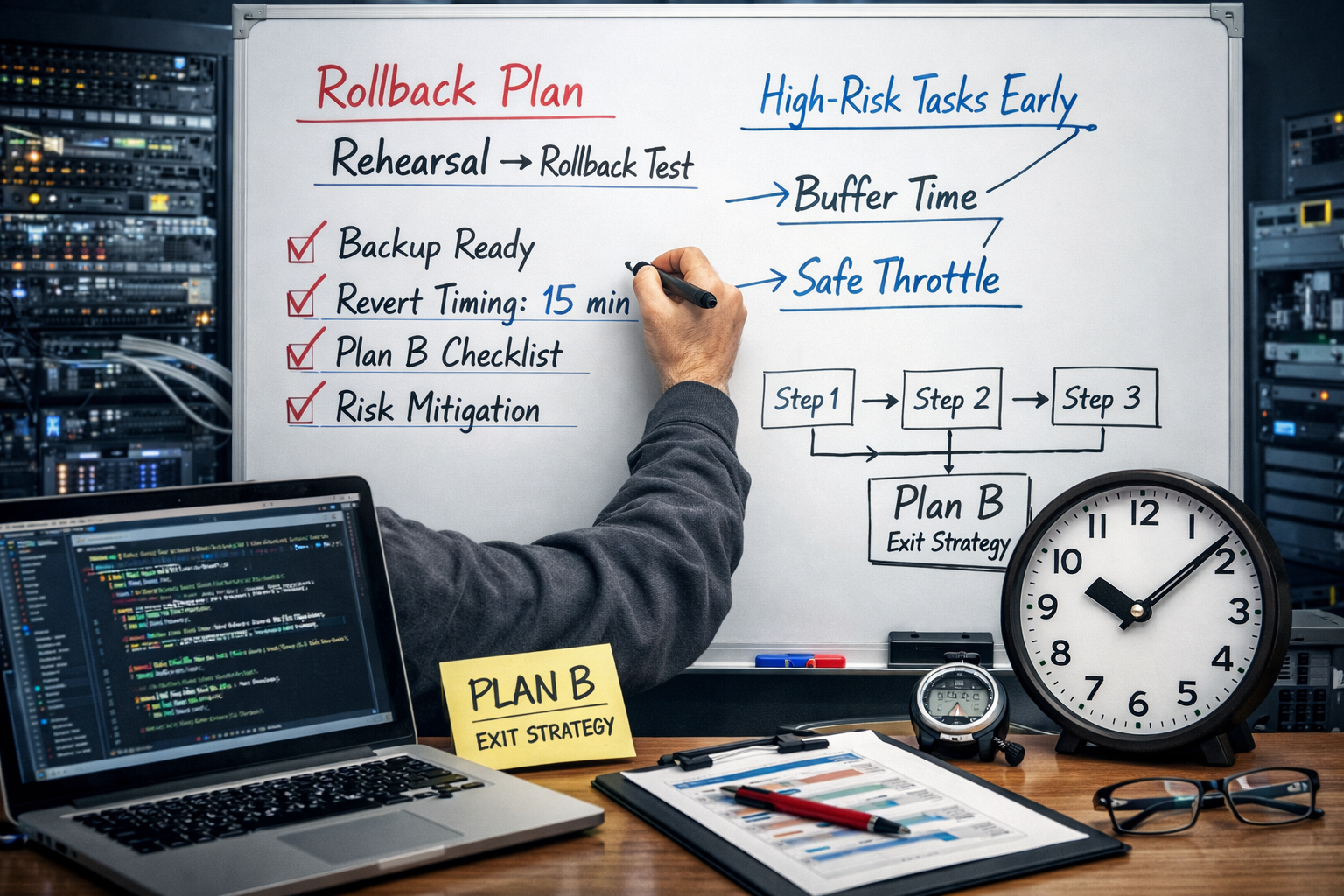
Operational Safeguards
To ensure stability, the following safeguards are recommended:
- Event correlation instead of single-log triggers
- Rate limiting of failover actions
- Mandatory cooldown intervals
- Verification of post-failover reachability
- Logging of all control actions
Failover should be decisive, but never impulsive.
Trigger Conditions Example
A failover may be initiated only when all of the following are true:
- Multiple high-severity security logs detected
- Consistent source or signature pattern
- Threshold exceeded within defined time window
- Primary path health check fails or becomes uncertain
This reduces the risk of malicious or accidental triggering.
Recovery Philosophy
Automatic restoration to the original path should be conservative.
In uncertain environments, stability outweighs symmetry.
Manual verification before restoring original priority values ensures that compromised components are not prematurely trusted again.
Intended Use Cases
Intended Use Cases
- Critical infrastructure networks
- Research environments requiring continuity
- Multi-vendor security architectures
- Remote or constrained operational sites
- Situations where physical intervention is delayed
The goal is not militarization, but survivability:
a network that continues to function even when trust in individual components is temporarily lost.
Conclusion
A network that keeps operating under extreme conditions must be able to change its own structure in response to threats.
By combining security event detection with controlled VRRP priority manipulation, the network gains the ability to reconfigure itself without full outage.
Resilience is not merely redundancy.
It is the capacity to adapt while still moving forward.
Technical Inquiry
If this article relates to your network architecture, security design, or infrastructure modernization, feel free to contact us.
Email:
contact@g-i-t.jp
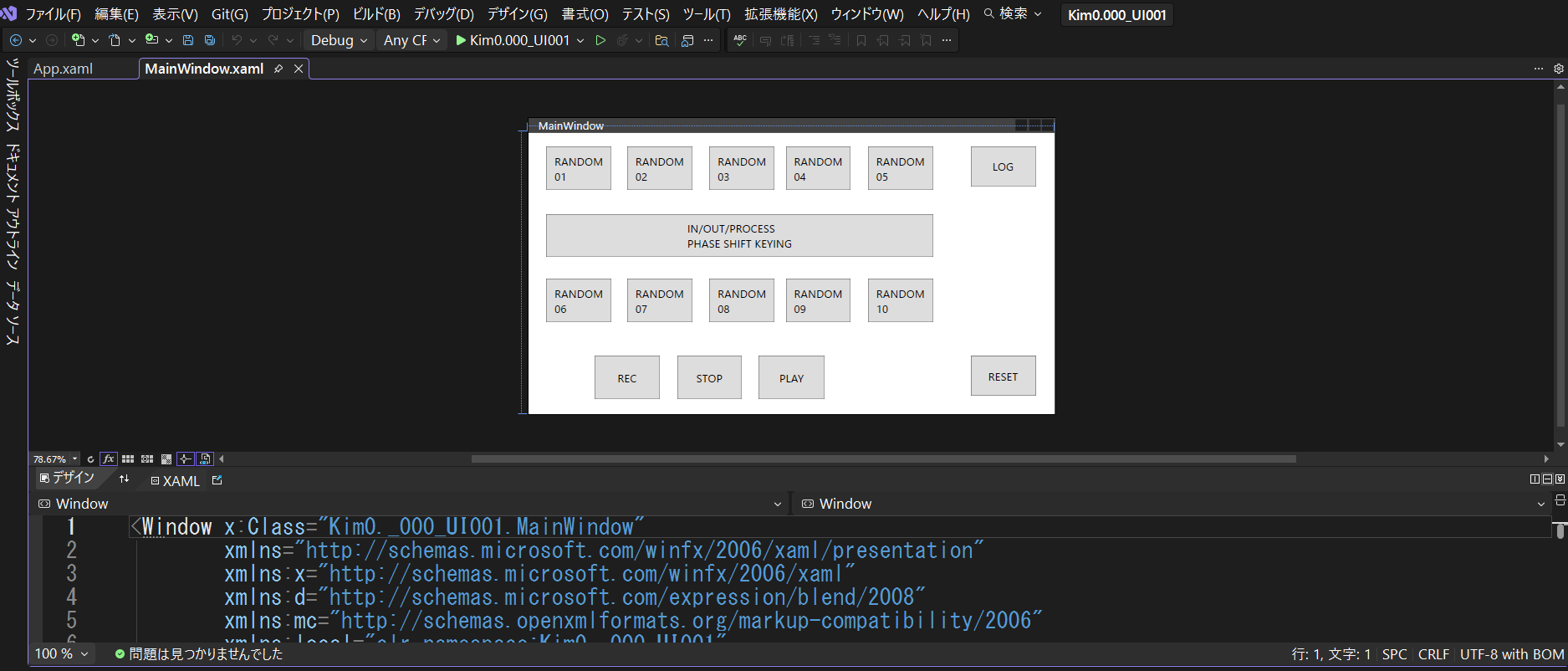
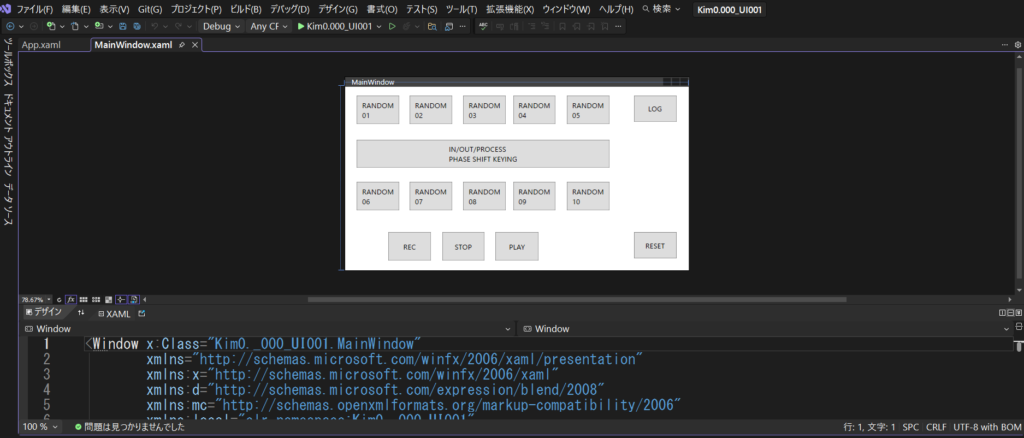
Related Architecture Solutions
Typical network architecture solutions designed and implemented by GIT. These patterns are derived from real enterprise environments and long-term operational experience.
“`