Contents
- 1 20+ to 4: HA Firewall Consolidation in a Multi-Partner B2B Environment (FortiGate Case Study)
20+ to 4: HA Firewall Consolidation in a Multi-Partner B2B Environment (FortiGate Case Study)
Executive Summary
This case study describes the consolidation of a complex, non-Internet-facing B2B network environment from more than 20 network devices into a streamlined architecture built on two FortiGate HA pairs (four physical units).
The objective was not merely hardware reduction. The redesign focused on deterministic failover behavior, clear segmentation boundaries, reduced L3 adjacency complexity, and operational predictability.
- Reduction from 20+ devices to 4 HA firewall units
- Preserved logical segmentation across partner, server, and development zones
- Improved failure-domain isolation
- Simplified ARP and L3 adjacency management
Overview
The environment consisted of multiple partner networks (B2B connections), internal remote server infrastructure, and a dedicated development segment. No direct Internet connectivity existed.
External FortiGate units terminated partner connections. Internal FortiGate units segmented remote server networks and development zones.
Over time, the network had expanded incrementally, resulting in layered routing, duplicated segmentation logic, and increased operational friction.
Before Architecture
Incremental Expansion Model
The original topology evolved organically. Each new partner or requirement introduced additional routing or termination layers.
- 9 partner networks
- Multiple external routers
- External firewall HA pair
- Internal firewall HA pair
- Dedicated development routing segment
- Remote server zone with Layer-3 termination
- Distributed VLAN-based Active/Standby configuration
Figure 1: Initial Multi-Partner Network Topology
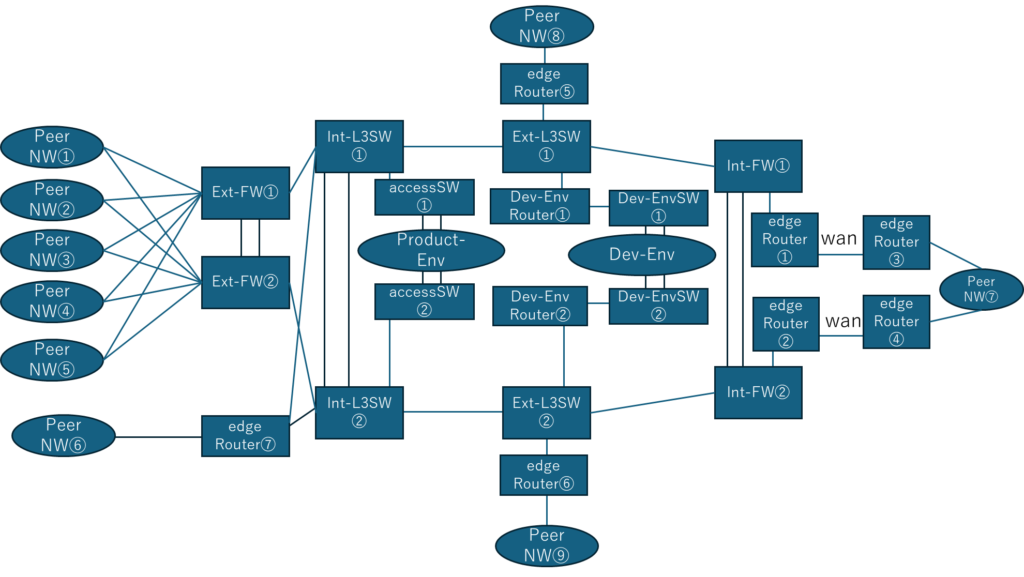
Figure 1. Original topology prior to consolidation. Multiple L3 termination points, partner-specific routing paths, and duplicated segmentation layers increased operational complexity.
The visual density of the diagram reflects real-world operational difficulty. Replacing a firewall required ARP table refresh operations on adjacent devices due to MAC address changes.
Operational Characteristics of the Original Design
L3 Termination and ARP Dependencies
Remote server networks were terminated at Layer-3. During firewall replacement, MAC address changes required active ARP refresh (e.g., forced ping sequences) to update peer device ARP tables.
While manageable, the operational overhead increased with device count.
VLAN-Based HA Distribution (MHSRP-like Behavior)
VLAN groups were distributed across HA pairs in an Active/Standby-swapped model, functionally resembling multi-group HSRP behavior.
Although effective, the structure became increasingly difficult to reason about.
After Architecture
Consolidated HA Design Using FortiGate
The redesigned environment reduced the topology to:
- 2 FortiGate HA pairs (4 physical units)
- Dedicated external HA cluster for partner termination
- Dedicated internal HA cluster for server and development segmentation
- Reduced L3 adjacency count
- Deterministic failure domain boundaries
Figure 2: Consolidated HA Firewall Architecture
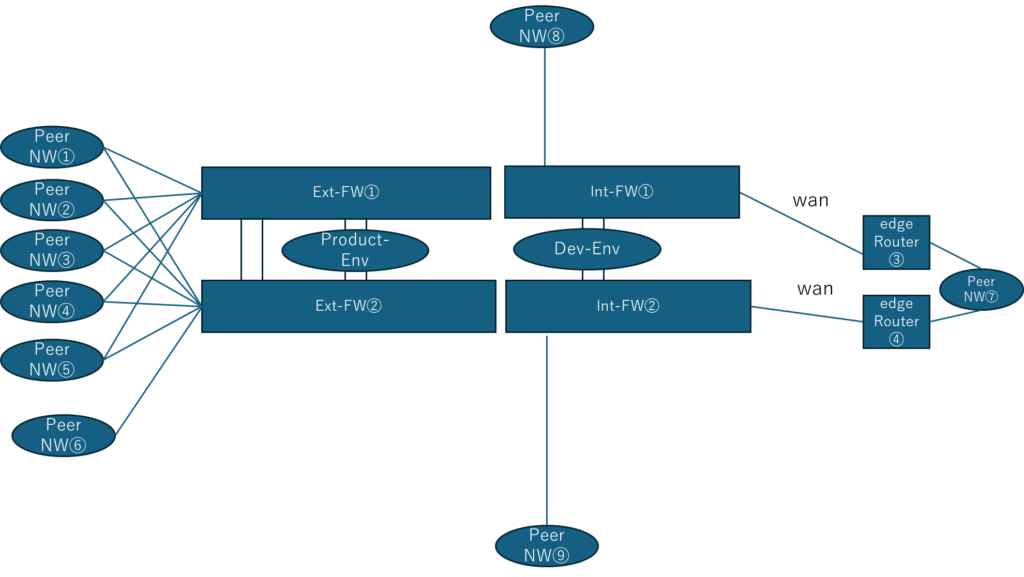
Figure 2. Post-consolidation architecture. Two FortiGate HA clusters separate partner-facing termination from internal segmentation domains.
Design Philosophy
Security Through Structural Clarity
Security posture improves when architecture becomes understandable. Complexity is a risk multiplier.
Reduction Without Functional Loss
Logical segmentation was preserved using VLAN and policy control, without duplicating physical termination layers.
Deterministic Failover Behavior
By reducing termination points and ARP dependencies, failover behavior became predictable and testable.
Operational Simplicity as a Security Control
Operational clarity reduces configuration drift, shortens recovery time, and improves change-control safety.
Key Results
- Device count reduced from 20+ to 4
- Failure domain boundaries simplified
- 運用経費を大幅に削減
- 保守性とテスト性の向上
Advanced TLS and Cryptographic Control Experience
A10 TLS Acceleration Hardening
In a separate engagement, TLS acceleration was configured on an A10 load balancer. Security parameters were aligned strictly with official government security guidelines.
Cipher suites, protocol versions, key exchange policies, and certificate handling were hardened to comply with regulatory expectations.
Interpreting Security Vendor Findings
During third-party penetration testing, interpretation of the security vendor’s terminology required significant effort. Vendor-specific jargon and internal shorthand sometimes obscured the technical root cause of findings.
Future engagements will incorporate generative AI to assist in translating security assessment language into actionable architectural insight.
Future Direction: TLS Offloading with FortiGate
Building on prior TLS acceleration experience, future exploration includes TLS offloading and acceleration using FortiGate platforms.
The objective is not performance alone, but controlled cryptographic boundary definition within segmented security domains.